The newest pages in the codewiki are:
Embedded programming in haskell using the Copilot stream DSL and Zephyr
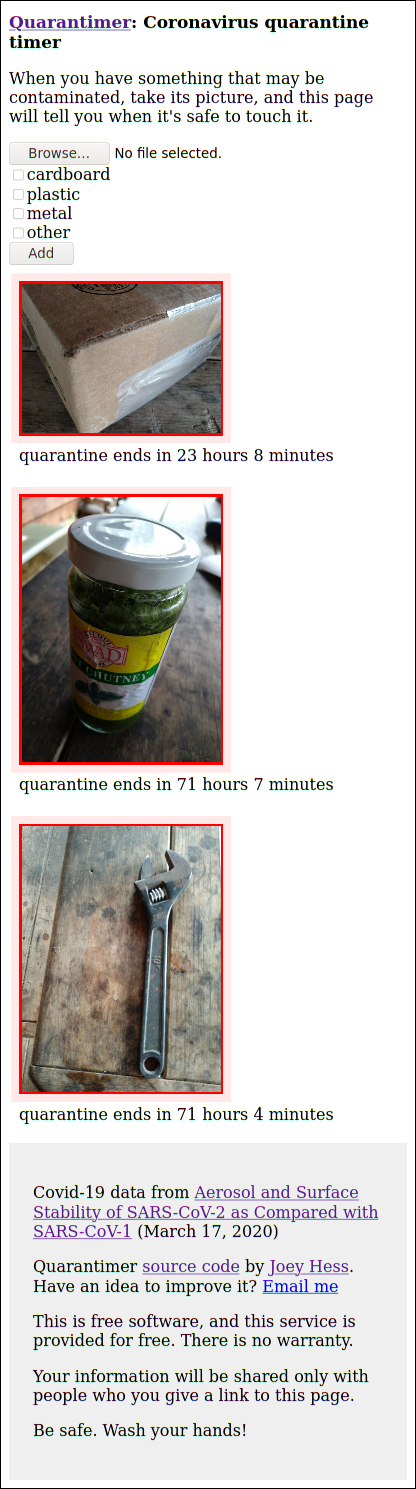
Coronavirus quarantine timer. It was built on a weekend and made available during the covid-19 pandemic, from March 23 2020 to March 15th 2021.
Transmission by fomites was eventually found to be uncommon, so the quarantimer probably didn't accomplish much beyond helping some people's peace of mind. In all it was used by 173 people, to track 401 objects.
Implemented in Haskell using the servant webserver, the code is available at https://git.joeyh.name/index.cgi/quarantimer.git/
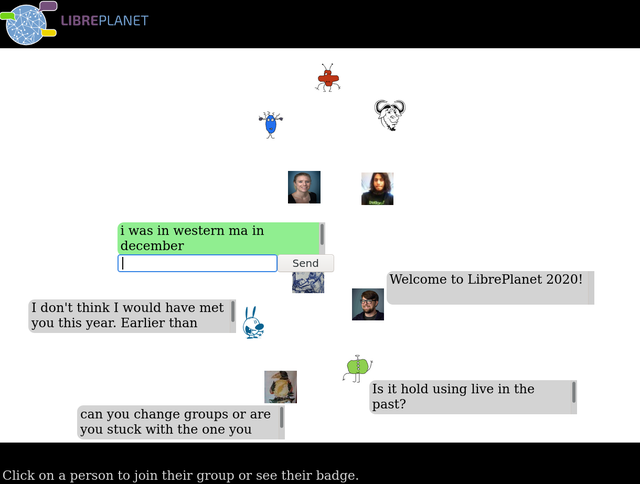
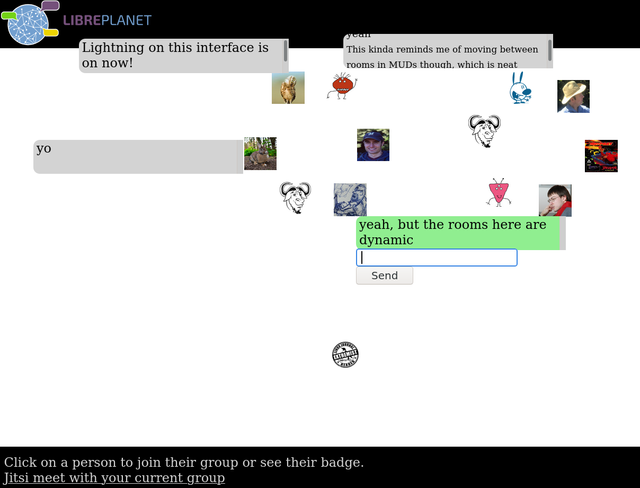
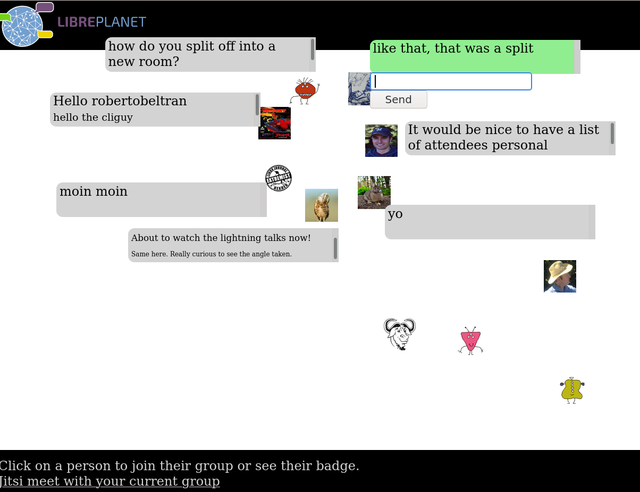
The best part of a good conference is its hallway track, with conversations in small groups that grow and split, and the chance to look around, find your friends and see what they're enthused about.
This program tries to emulate that in a virtual space. It's experimental and has only been used in conjunction with one conference so far.
Arduino programming in haskell using the Copilot stream DSL
haskell library like filepath but for RawFilePaths.